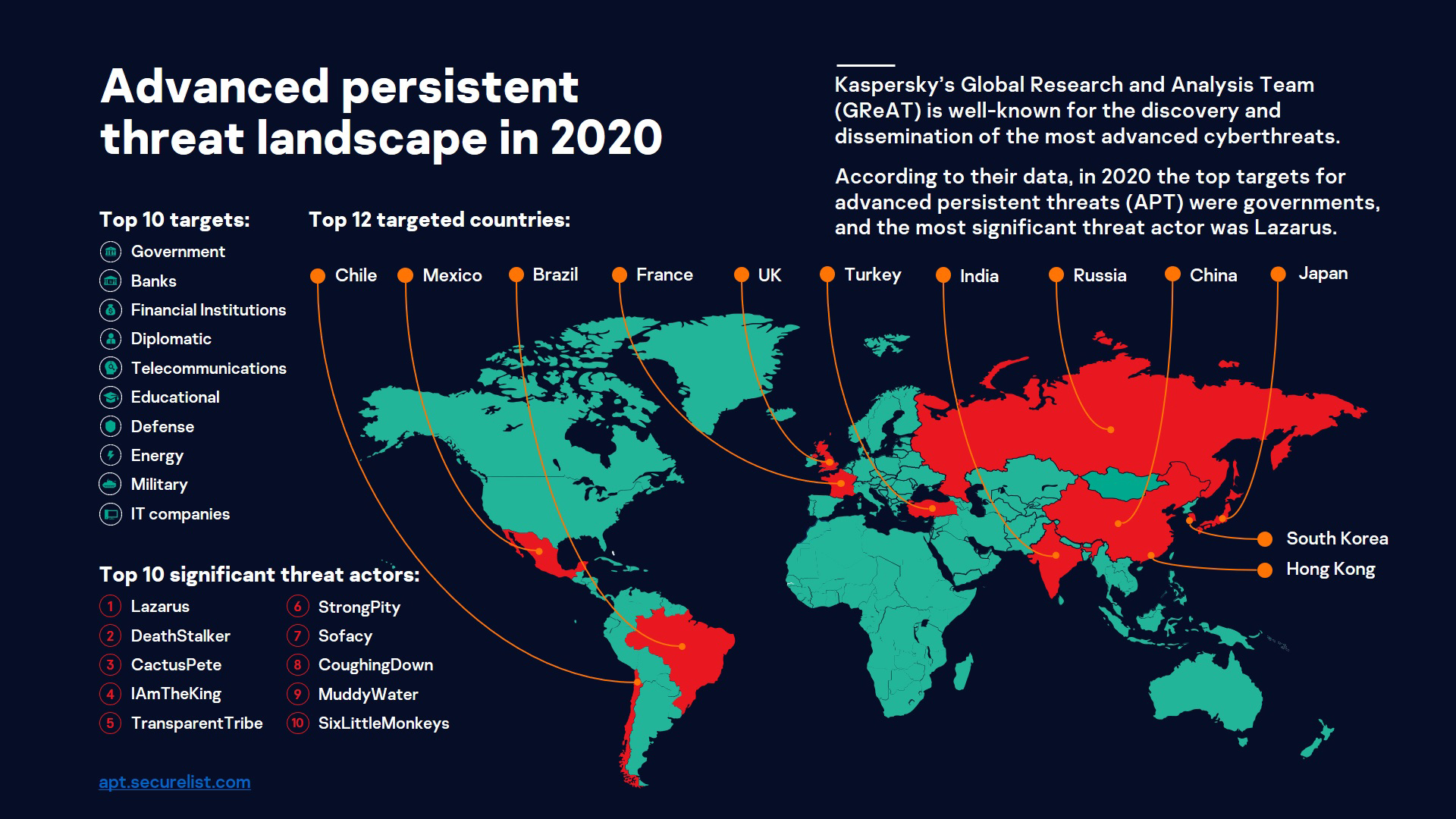
Advanced Persistent Threats in 2021: Kaspersky Researchers Predict New Threat Angles and Attack Strategies to Come | Business Wire

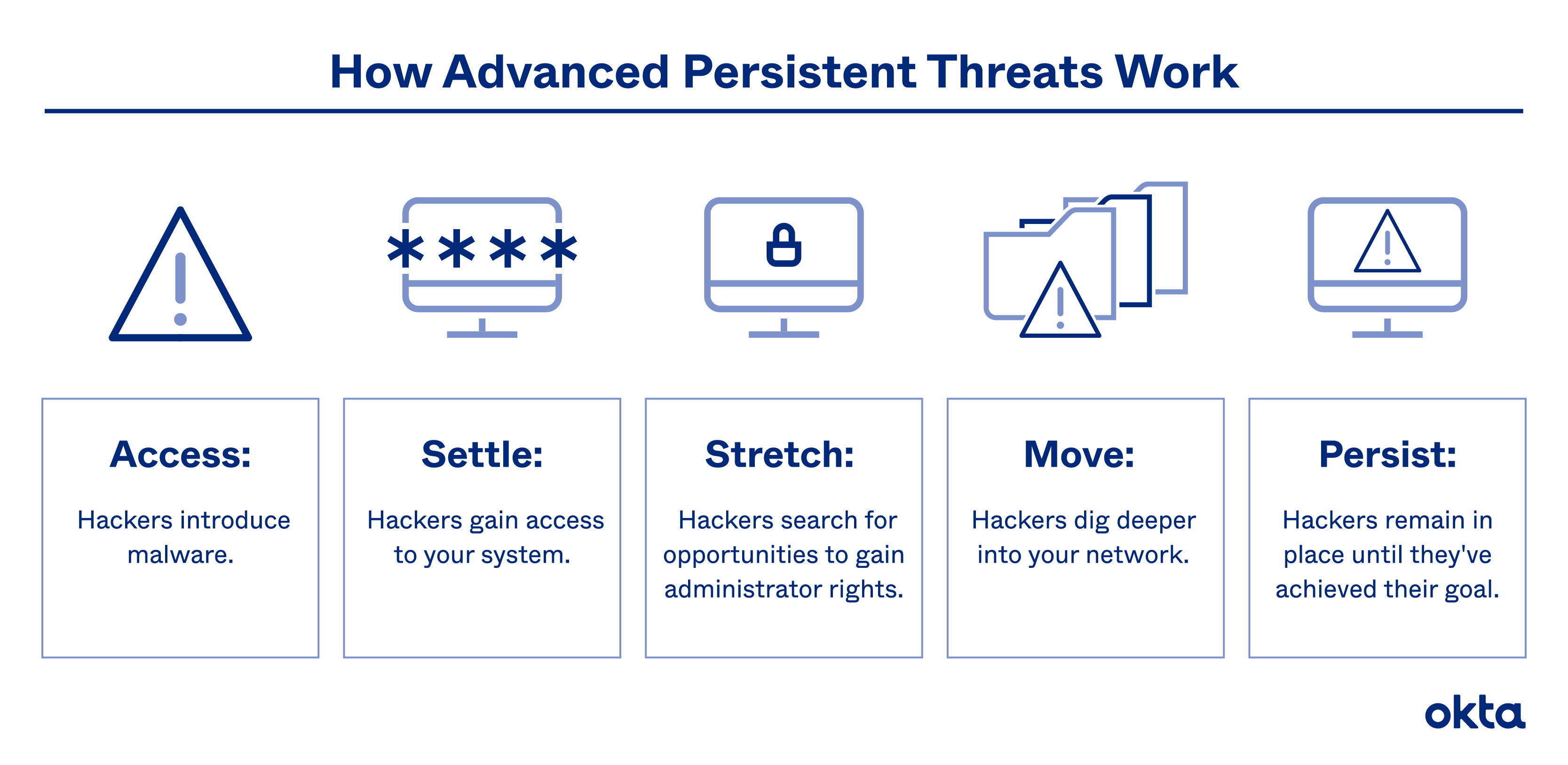
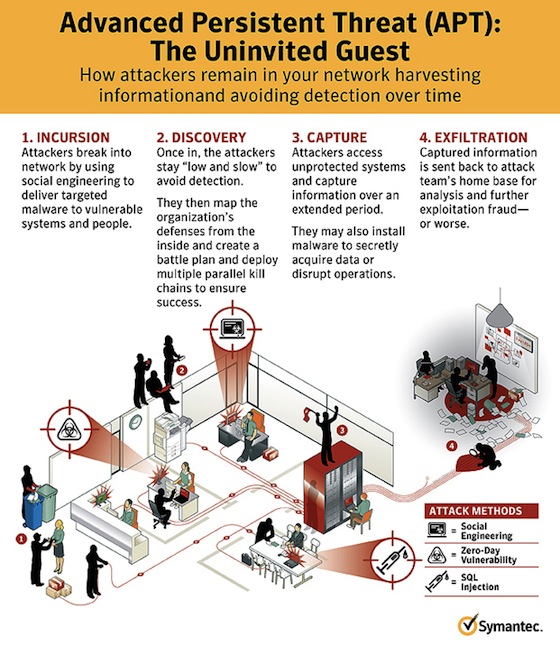
What is Advanced Persistent Threat? Definition, Lifecycle, Identification and Management Best Practices | Spiceworks
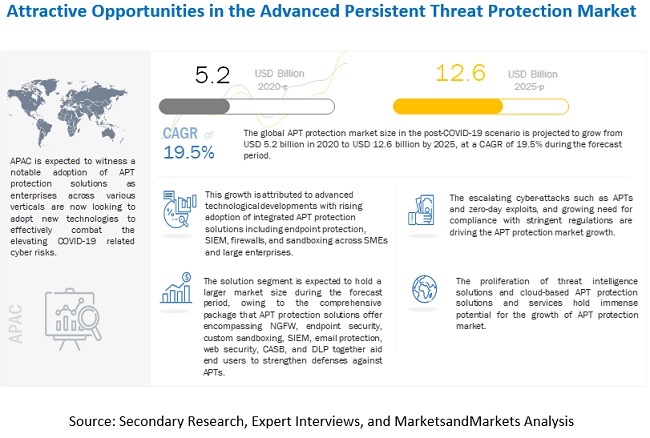
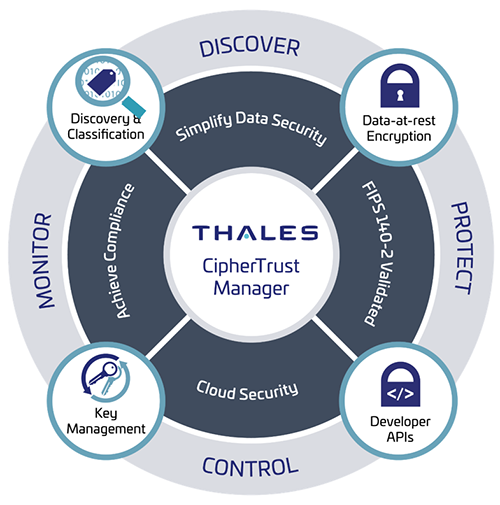
Advanced Persistent Threat Protection Market Size, Share and Global Market Forecast to 2025 | MarketsandMarkets
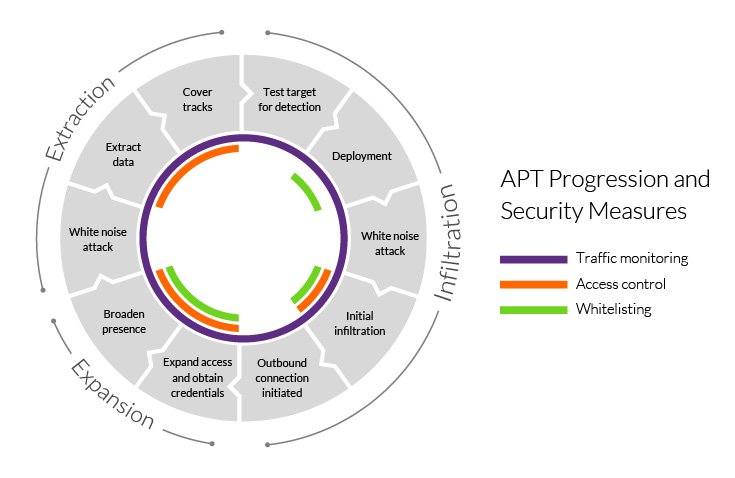
![PDF] Advanced Persistent Threats Attacks in Cyberspace. Threats, Vulnerabilities, Methods of Protection | Semantic Scholar PDF] Advanced Persistent Threats Attacks in Cyberspace. Threats, Vulnerabilities, Methods of Protection | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/310d9b72a7e84f44fca66bbf3a9f25ce4f87a3d4/2-Figure1-1.png)
PDF] Advanced Persistent Threats Attacks in Cyberspace. Threats, Vulnerabilities, Methods of Protection | Semantic Scholar
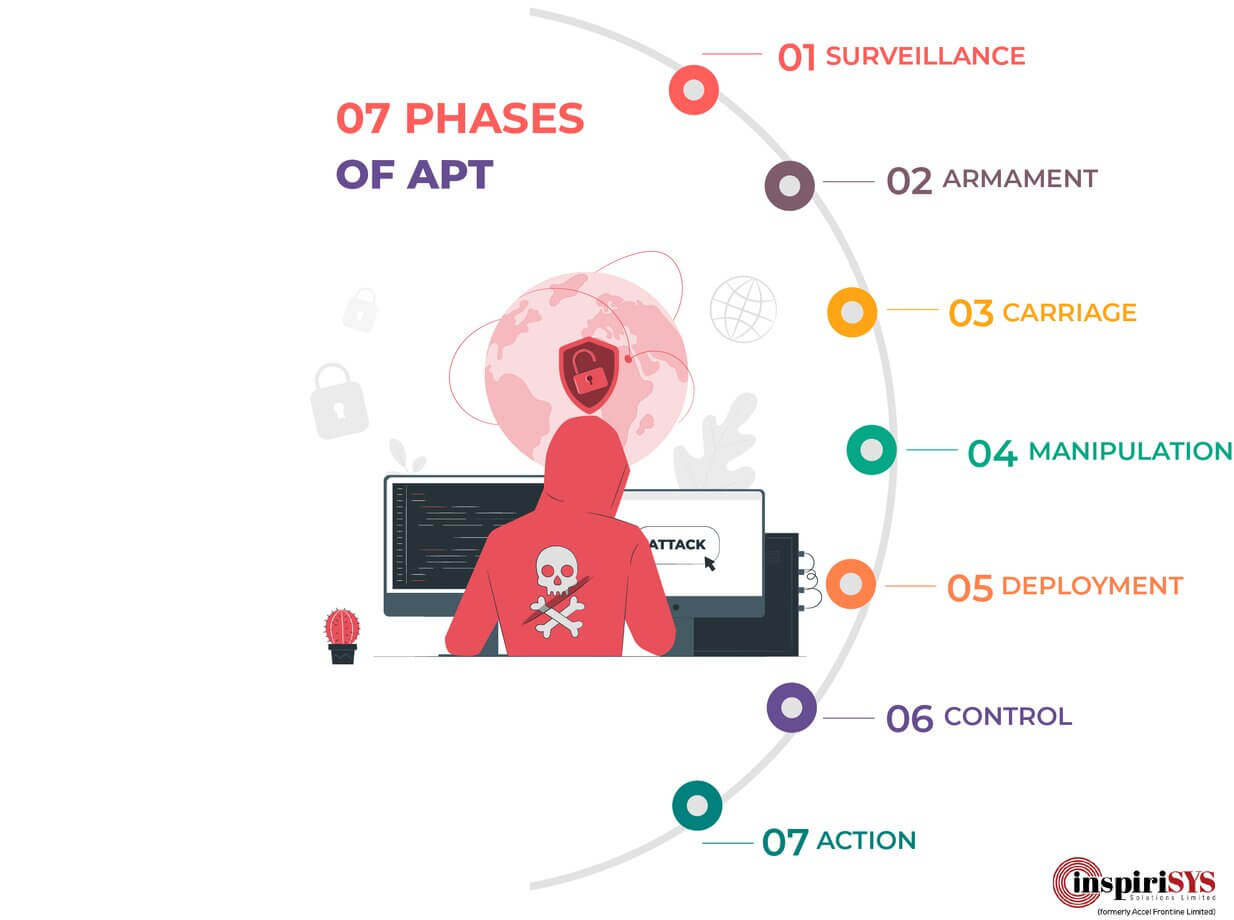
![PDF] Advanced Persistent Threat ( APT ) Beyond the hype Project report in IMT 4582 Network security at Gjøvik University College during spring 2013 | Semantic Scholar PDF] Advanced Persistent Threat ( APT ) Beyond the hype Project report in IMT 4582 Network security at Gjøvik University College during spring 2013 | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/a140cd962b136474685db82de60bb15f4fe1d7e1/8-Figure1-1.png)
PDF] Advanced Persistent Threat ( APT ) Beyond the hype Project report in IMT 4582 Network security at Gjøvik University College during spring 2013 | Semantic Scholar